Idealstack connects to your AWS account
& creates a modern best-practice cluster
for hosting PHP-based apps and websites
Idealstack is totally different from every other hosting platform out there. It's not a clone of godaddy or cpanel, and it doesn't just dump Nginx and PHP on a server and sell it to you. It's a complete rethinking of how to host PHP-based apps and websites
Idealstack helps you set up a modern best-practice AWS stack
There’s a lot of tools out there that will manage a server on AWS or other cloud platforms.
Idealstack doesn’t just manage a server, it manages a Stack, made out of 25+ different AWS services. We help you do things “the way they should be done” on AWS, inspired by the principles of the AWS Well Architected Framework
Don't just setup a server
Run a modern best-practice cluster
- Self-healing clusters across multiple availability zones
- Autoscaling based on demand
- Built from native AWS services - Cloudformation, RDS, ECS
- Managed OS Security Updates
How Idealstack implements AWS best practices
<?php //How do I use highly-available sessions across my cluster using DynamoDB? // It happens automatically, just use normal PHP session functions: session_start(); $_SESSION['Normal Session Stuff'] = 'Easy!'; //How do I send email using AWS's Simple Email Service? // Just use normal PHP mail functions: mail('joe.blogs@example.com', "Here's an email through SES!", "Just sent you this with the normal PHP mail command"); //How do I read and write files on a highly-available clustered file store? // Just use normal PHP file IO: $file_contents = file_get_contents("myfile.txt"); file_put_contents("myfile.txt", "How easy was that"); //How do I connect to a clustered, highly available mysql-compatible database? // Idealstack sets all this up for you, // including the alias 'database' for your db hostname $mysqli = new mysqli('database', 'your_user', 'your_pass', 'your_db'); //How do I compress and minify the output of my PHP // app to get higher performance and google rank? // mod_pagespeed does it automatically: echo "<!-- Do nothing, it happens automatically with google's mod_pagespeed -->"; //How do I make my app autoscale? // It'll happen automatically: $todo = null;
No need to change your code
Idealstack
can cluster-enable any PHP app, while still letting it take advantage of the power of AWS.
It does this by supporting all the normal PHP functions but transparently mapping them to
the appropriate AWS services.
You don't need to change your code or use the AWS API, and this also means you can run any
PHP app like Wordpress, Laravel apps, or your own custom code, even legacy apps.
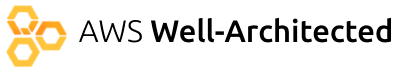
No changes needed to your developer workflow
You don’t need to retrain or spend months learning new tools to use idealstack. It works like the familiar hosting consoles that PHP developers are used to:
- Create and manage sites in an easy to use GUI
- Upload files over SFTP or an easy web-based GUI
- Connect over SSH to run commands
- Manage databases using a web-based GUI
- No need to manage servers. Operating system images and updates are handled by idealstack
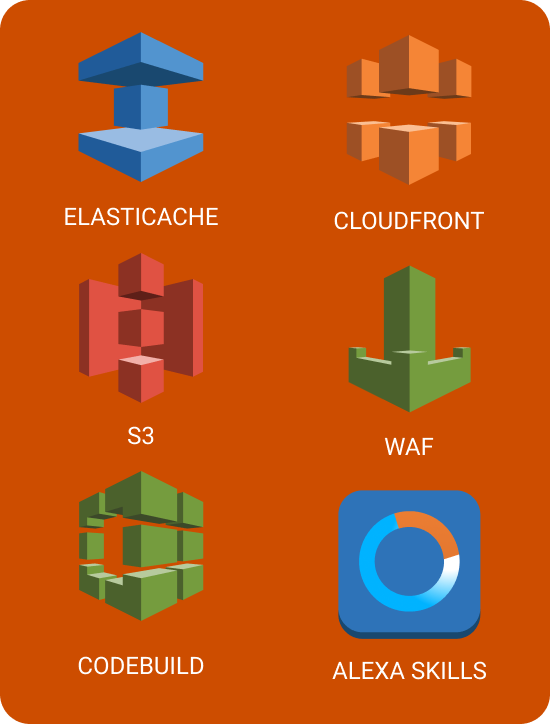
Connect to AWS services
Because Idealstack runs in your own AWS account, you can easily connect your sites and apps to any other AWS service. The possibilities are endless:
- Cloudfront CDN lets you accelerate the performance of websites
- ElasticCache provides fully-managed Redis or Memcache instances to provide caching for your sites
- ElasticSearch provides a powerful search engine that can be integrated into many PHP-based CMS and Ecommerce systems
- AWS WAF can protect your site against attacks S3 provides cheap and ultra-reliable storage
- Use your client's log data to create metrics, dashboards and alerts with the click of a few buttons using CloudWatch.
- Test & deploy your code using AWS Codebuild
- Create Alexa skills that interact with your websites and apps
What will my AWS costs be?
Idealstack can run within the AWS free tier for a minimal stack. We’ve put together a few more examples on our Pricing Page
How many sites/apps can I host?
All Idealstack plans support unlimited sites. By using enough stacks and large enough instances and enough of them you can host as many as you want, including a mix of large and small sites. To get an idea of how many sites typical AWS setups will accomodate, check out our stack sizing guide
What about security?
Idealstack uses containerisation technology to isolate sites, rolls out OS security updates automatically, and is designed using a best-practice approach to security
Read more about our approach to security
Does Idealstack provide SSL certificates, domain names, email hosting etc
You can register these for some of the best prices in the industry via AWS services. Where appropriate Idealstack integrates to these services to simplify things
Get Started with Idealstack for free
Connect Idealstack to your AWS account and give it a go. Idealstack can run within the limitations of the AWS Free Tier so if you aren't on AWS yet, signup now and trial it for free.